An AWS automation script rarely fails on Azure loudly. There’s no dramatic error message announcing architectural incompatibility. Instead, it fails quietly as resources don’t tag correctly, budgets don’t trigger, scaling logic behaves unpredictably, or cost controls simply stop working. And that’s what makes the multi-cloud trap so dangerous.
The multi-cloud environment promises portability, vendor leverage, and resilience, which sounds irresistible. But in practice, multi-cloud automation breaks down the moment teams assume that AWS automation scripts will mostly work on Azure. They won’t. And not because your engineers made mistakes but because the two clouds are fundamentally different at the control-plane level. This article breaks down why AWS automation scripts fail on Azure, where most teams go wrong, and how to fix automation without doubling operational complexity or rebuilding everything from scratch.
The Illusion of Cloud Parity
From the outside, AWS and Azure appear similar. Both offer compute, storage, networking, IAM, monitoring, and automation frameworks. Both claim to support infrastructure-as-code, policy enforcement, and cost governance. This surface-level similarity is exactly what leads teams into the multi-cloud trap.
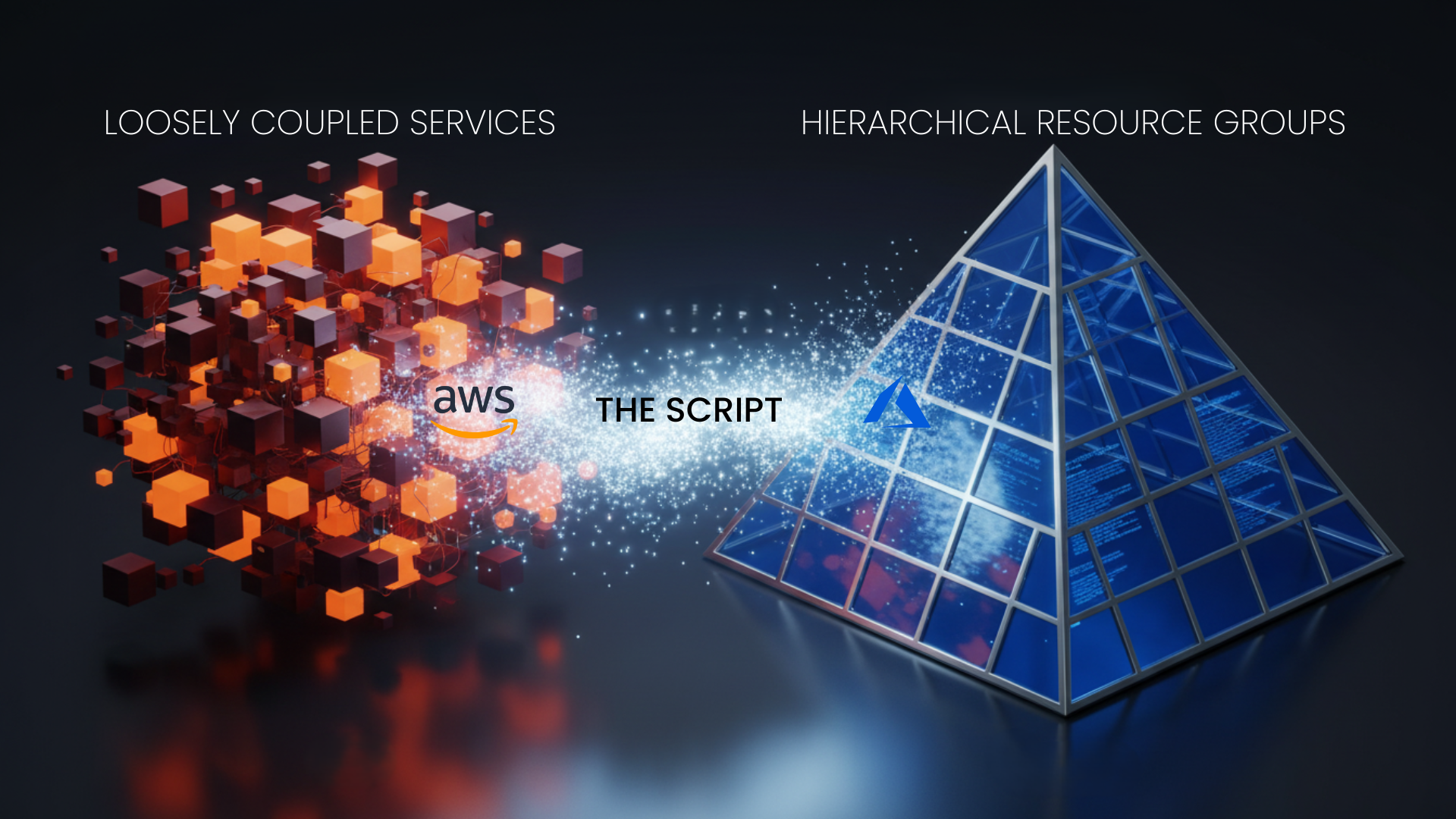
Underneath, however, AWS and Azure evolved from entirely different architectural philosophies. AWS was built as a collection of loosely coupled services with granular primitives. Azure, by contrast, evolved from enterprise Windows and Active Directory roots, emphasizing centralized resource management and policy inheritance. This difference matters profoundly for automation.
Why AWS Automation Scripts Break on Azure?
Resource Models Are Structurally Different
AWS automation scripts are often written around individual services like EC2, S3, Lambda, and IAM, each with its own independent lifecycle. Azure, however, organizes everything inside Resource Groups, which act as both logical and governance boundaries. An AWS script that assumes it can tag, delete, or modify a resource independently often fails in Azure because:
Azure policies may block changes at the Resource Group level
Resource dependencies are enforced more strictly
Inheritance rules override script-level actions
This is why AWS tagging automation frequently runs successfully on Azure yet produces incomplete or non-compliant results.
Identity and Access Automation Does Not Translate
AWS IAM is identity-centric and role-based at a granular service level. Azure IAM is deeply tied to Azure Active Directory, subscriptions, and management groups.
An AWS script that dynamically creates roles, assigns policies, or rotates credentials often breaks on Azure because:
Azure RBAC scopes operate hierarchically
Permissions propagate differently across subscriptions
Role assignments are not service-native but directory-centric
According to Microsoft documentation, Azure role propagation delays alone can take minutes, which silently breaks automation pipelines expecting immediate consistency.
Monitoring and Metrics are not Equivalent
CloudWatch metrics in AWS are pull-based and service-scoped. Azure Monitor metrics are push-based and tightly integrated into platform telemetry. Automation scripts that depend on CPU thresholds, cost anomaly triggers and scaling metrics that often behave unpredictably when ported directly to Azure because metric namespaces, aggregation windows, and alert semantics differ. This is one reason cost-control scripts that work flawlessly in AWS suddenly miss Azure cost spikes entirely.
The Cost Automation Failure
The most damaging automation failures aren’t infrastructure failures, but they’re financial blind spots. AWS cost automation scripts often rely on CUR (Cost and Usage Reports), service-level tagging enforcement, and account-based budget alerts
Azure uses a completely different cost ingestion and attribution model. Costs roll up at the subscription and management group level, and tagging behavior is enforced via Azure Policy, not best-effort scripts. This is where AWS-centric automation fails hardest because cost automation isn’t portable.
Infrastructure-as-Code Doesn’t Help
Many teams assume Terraform or Bicep will solve automation portability. They help, but they don’t fix the underlying problem. Terraform abstracts provisioning syntax, not cloud behavior. A Terraform plan that deploys cleanly in AWS and Azure can still produce radically different operational outcomes.
For example:
Autoscaling groups behave differently under load
Budget enforcement triggers at different billing stages
Idle resource detection requires different logic
This is why teams end up with parallel automation logic, one set of scripts tuned for AWS behavior, another for Azure. That’s not multi-cloud efficiency; it’s duplicated complexity.
The Real Fix
The only sustainable way out of the multi-cloud trap is to stop writing automation that assumes cloud primitives behave the same. Instead, successful teams separate automation into three distinct layers, even if they don’t formally name them:
Intent Layer – what you want to happen (e.g., “prevent spend spikes,” “enforce tagging,” “limit non-prod scaling”)
Policy Layer – the rules that define acceptable behavior
Execution Layer – cloud-specific implementations
AWS automation scripts usually collapse all three into one. Azure punishes that assumption. When intent and policy are abstracted away from execution, automation becomes portable, even if the execution logic remains cloud-specific.
Why Platform-Level Automation Wins Multi-Cloud?
This is exactly why many enterprises are moving away from script-heavy automation and toward platform-level governance and intelligence layers. Instead of writing scripts that poll billing APIs, interpret cost anomalies, and enforce budget rules manually, they use platforms that normalize data across clouds and apply policy-driven automation consistently, regardless of provider differences.
This is where tools like Atler Pilot fit naturally, not as a replacement for cloud-native tooling, but as a control plane above it. By analyzing spend patterns, detecting anomalies in real time, and enforcing governance rules across AWS and Azure uniformly, teams avoid duplicating logic while still respecting cloud-specific behaviors. The result is fewer brittle scripts and far less operational debt.
How to Fix AWS-to-Azure Automation Without Rewriting Everything?
The fix is not rewritten for every script. It’s changing what scripts are responsible for. Teams that succeed do three things consistently. They stop using scripts as decision-makers. They centralize cost and policy intelligence instead of embedding logic in cloud-specific tooling. And finally, they measure automation success by outcomes, not by script execution success. This is why many mature organizations now treat cloud automation as policy enforcement, not procedural scripting.
Conclusion
AWS automation scripts break on Azure because AWS and Azure are not interchangeable systems. They differ in identity models, resource hierarchies, cost attribution, and governance enforcement. Treating them as variations of the same cloud guarantees failure. The fix isn’t abandoning automation, but it’s evolving it. By separating intent from execution, centralizing cost intelligence, and relying less on brittle scripts, teams can finally make multi-cloud work without multiplying complexity. And in an era where cloud APIs change faster than internal teams can track, automation that adapts automatically is the best survival technique.
All in One Place
Atler Pilot decodes your cloud spend story by bringing monitoring, automation, and intelligent insights together for faster and better cloud operations.